Cyberattacks a growing threat
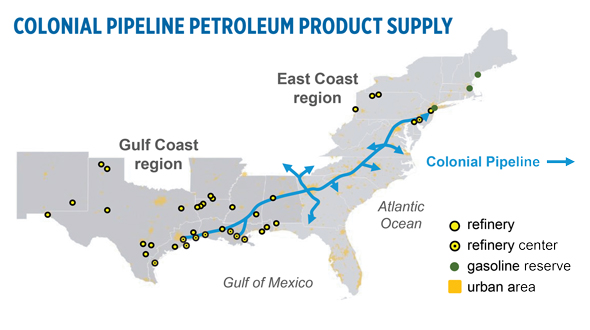
The Colonial Pipeline transports refined petroleum products. (Source: U.S. Energy Information Administration)
The world awoke to a catastrophic ransomware attack Mother’s Day weekend by what is reported to be a criminal operation out of Russia. The pipeline was held for ransom and was not fully operational for about a week. This pipeline extends from Texas to New Jersey and is one of the nation’s major routes for refined petroleum products.
The attack wreaked havoc on fuel supplies in the Southeast and along the East Coast, and prices soared as a result. News outlets reported that Colonial Pipeline paid $4.4 million to the hackers to remove the ransomware.
This event is not new. Ransomware is a recurring problem in industries today. A recent survey of 125 midstream oil and gas companies conducted by law firm Jones Walker found that 40 percent of these companies reported an attempted or successful data breach of their information technology systems in a 12-month period. Yet, only 7 percent had updated or improved their written security policies. Only 38 percent were planning to update their security policies.
Given the reality that more employees are working remotely, this security risk is heightened. I am confident that if a similar survey was conducted of propane industry members, the results would be similar.
The vast majority of oil and gas pipelines in the U.S. are owned by private companies. There is little to no collaboration among these companies to share best practices on how to protect against this real and ever-growing security threat. The propane industry is similar in that it is composed of mainly small- to medium-size private businesses.
These risks in the oil and gas pipeline industry can adversely affect the propane industry. Our product is also shipped via pipeline to terminal points around the country. What would a ransomware attack do to fuel supplies during the height of the heating season? What about during a heating season like we experienced in 2013-14? The results for marketers and their customers could be devastating.
With this ransomware attack fresh in our minds, the industry needs to be proactive in finding ways to minimize cybersecurity threats all along the distribution chain.
This likely calls for planning at the national level by the National Propane Gas Association or Propane Education & Research Council. Developing best practices to thwart cyberattacks along the supply chain will require input from all stakeholders.
Most fuel supply agreements along the supply chain have a force majeure clause. The language of your force majeure clause needs to be analyzed in light of the threat of ransomware attacks and loss of fuel supply. Does the force majeure clause cover this type of event? Does the clause adequately or fairly allocate the risk related to such an event?
Does your insurance provide coverage for a cyberattack? Check with your insurance agent. Understand the limitations of coverage if it exists. According to the Jones Walker study, about 74 percent of the midstream gas companies it surveyed did not have insurance for cyberattacks.
Industry needs to self-regulate or you can be certain the government will step in. In 2016, Congress passed the Protecting our Infrastructure of Pipelines and Enhancing Safety Act. No regulations have been implemented under this act yet. Given these developments, we can expect regulations soon. President Joe Biden signed an executive order to deal with this growing threat. Congress is already making noise about creating new laws. To avoid the imposition of regulations that are well-meaning but miss the mark, industry needs to step up and create its own best practices.
John V. McCoy is with McCoy, Leavitt, Laskey LLC. His firm represents industry members nationally. He can be reached at jmccoy@MLLlaw.com or at 262-522-7007.